Difference between revisions of "WormNAT2"
From Worms Knowledge Base
m |
(Added translations) |
||
| (8 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
{{ParentArticle|[[WormKit]]}} | {{ParentArticle|[[WormKit]]}} | ||
| + | {{Languages|en|WormNAT2|ru|WormNAT2/ru}} | ||
| + | {{Software_infobox | ||
| + | | icon = WormNAT.gif | ||
| + | | name = WormNAT 2 | ||
| + | | developer = [[People/CyberShadow|CyberShadow]] | ||
| + | | version = 2.3 / August 22, 2015 | ||
| + | | games = [[Worms Armageddon|W:A]] | ||
| + | | waver = 3.6.28.0+ | ||
| + | | language = Delphi | ||
| + | | license = [https://github.com/CyberShadow/WormKit Open-source] | ||
| + | | download = [http://worms.thecybershadow.net/wormkit/wkWormNAT2.zip wkWormNAT2.zip (92 KB)] | ||
| + | }} | ||
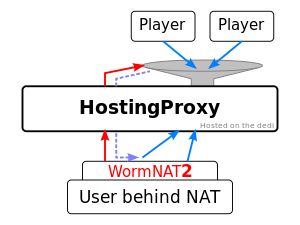
[[Image:WormNAT2.svg|thumb|A crude drawing of how WormNAT2 works]] | [[Image:WormNAT2.svg|thumb|A crude drawing of how WormNAT2 works]] | ||
[[WormNAT2]] is a [[WormKit]] module which enables players behind NAT or firewalls to host games which are joinable by everyone. It is a rewrite of the first WormNAT module, which required extensive configuration and that all players have the module installed. | [[WormNAT2]] is a [[WormKit]] module which enables players behind NAT or firewalls to host games which are joinable by everyone. It is a rewrite of the first WormNAT module, which required extensive configuration and that all players have the module installed. | ||
The advantages of WormNAT2 over WormNAT / [[HostingBuddy]] / Hamachi: | The advantages of WormNAT2 over WormNAT / [[HostingBuddy]] / Hamachi: | ||
| − | * very easy to set up ( | + | * very easy to set up (extract WormNAT2 DLLs to W:A folder, enable "Load WormKit modules" in Advanced Settings) |
* no configuration is necessary | * no configuration is necessary | ||
* anyone can join games hosted with WormNAT2 | * anyone can join games hosted with WormNAT2 | ||
| Line 10: | Line 22: | ||
== How it works == | == How it works == | ||
| − | WormNAT2 works by asking a ''reverse proxy'' (which is running the HostingProxy software) to host the game for the player. A control connection is opened to the proxy server, '''proxy. | + | WormNAT2 works by asking a ''reverse proxy'' (which is running the HostingProxy software) to host the game for the player. A control connection is opened to the proxy server, '''proxy.wormnet.net''' on port 9301. As soon as the connection is established, the proxy assigns a port for the game and sends back the port number through the control connection. WormNAT2 creates the game at the address '''proxy.wormnet.net:''port'''''. |
Once the game is created, every time a new player connects to the proxy, the proxy creates a new listening port for WormNAT2 and sends the port number through the control connection. WormNAT2 then connects to the specified port; the proxy then proceeds to route data between the two connections. | Once the game is created, every time a new player connects to the proxy, the proxy creates a new listening port for WormNAT2 and sends the port number through the control connection. WormNAT2 then connects to the specified port; the proxy then proceeds to route data between the two connections. | ||
Internally, WormNAT2 operates by monitoring [[WormNET]] game creation and closing. Incoming connections are simulated by creating actual connections from within the same process, and routing the data between those connections and connections to the proxy server. | Internally, WormNAT2 operates by monitoring [[WormNET]] game creation and closing. Incoming connections are simulated by creating actual connections from within the same process, and routing the data between those connections and connections to the proxy server. | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
== See also == | == See also == | ||
* [[Hosting Guide]] | * [[Hosting Guide]] | ||
* [[HostingBuddy]] | * [[HostingBuddy]] | ||
Revision as of 18:32, 7 February 2016
| Developer: | CyberShadow |
|---|---|
| Latest version: | 2.3 / August 22, 2015 |
| Supported games: | W:A |
| Supported W:A version: | 3.6.28.0+ |
| Language: | Delphi |
| License: | Open-source |
| Download: | wkWormNAT2.zip (92 KB) |
WormNAT2 is a WormKit module which enables players behind NAT or firewalls to host games which are joinable by everyone. It is a rewrite of the first WormNAT module, which required extensive configuration and that all players have the module installed.
The advantages of WormNAT2 over WormNAT / HostingBuddy / Hamachi:
- very easy to set up (extract WormNAT2 DLLs to W:A folder, enable "Load WormKit modules" in Advanced Settings)
- no configuration is necessary
- anyone can join games hosted with WormNAT2
- games are hosted as usual, there is no need to configure the game settings with tedious text commands
How it works
WormNAT2 works by asking a reverse proxy (which is running the HostingProxy software) to host the game for the player. A control connection is opened to the proxy server, proxy.wormnet.net on port 9301. As soon as the connection is established, the proxy assigns a port for the game and sends back the port number through the control connection. WormNAT2 creates the game at the address proxy.wormnet.net:port.
Once the game is created, every time a new player connects to the proxy, the proxy creates a new listening port for WormNAT2 and sends the port number through the control connection. WormNAT2 then connects to the specified port; the proxy then proceeds to route data between the two connections.
Internally, WormNAT2 operates by monitoring WormNET game creation and closing. Incoming connections are simulated by creating actual connections from within the same process, and routing the data between those connections and connections to the proxy server.